Cryptocurrency Virus Threatens Facebook Users, Gets Shut Down Before Causing Damage

The fully-digital nature of cryptocurrencies makes the asset class highly susceptible to online crimes, phishing, and the computer industry’s most dreaded threat; hacking. As the popularity of digital asset continues to grow, hackers and cyber-thieves find new, innovative methods to steal cryptocurrencies, usually without alerting the victim in any manner.
Facebook Messenger Faces Hacker’s Wrath
The latest mobile app to be compromised for “cryptojacking” is the globally popular Facebook App, including its ‘Messenger’ platform. According to reports, a new computer virus, called FacexWorm, injects Facebook, Google Chrome, and FB Messenger with a malware code that allows devious hackers to gain information of the victim’s social passwords, cryptocurrency account details, while also running a crypto-mining script in the background; without any permission of the user.
The virus, called FacexWorm, was discovered in April 2018 by researchers at Trend Micro, a Japanese cybersecurity firm.
As per Trend Micro, the FacexWorm virus is related to 2017’s malicious facebook spam campaigns – which took place in August 2017 and December 2017 – and injected victims with the ‘Digmine Virus,’ which borrowed the computer’s processing power to mine cryptocurrency.
According to Trend Micro:
“FacexWorm’s modus operandi is similar to the previous two campaigns, but with the addition of new techniques aimed at cryptocurrency users.”
An Elaborately Planned Malware
The process of injecting the virus is straightforward and raises no obvious alarms for the unsuspecting victim. However, the malware collects user data in a number of ways.
The infection chain starts with unsuspecting users receiving a “spam” link on their Messenger app, which leads to a fraudulent YouTube page upon clicking. Post this, users are asked to download a Chrome extension, which supposedly helps with better functioning of the YouTube platform.
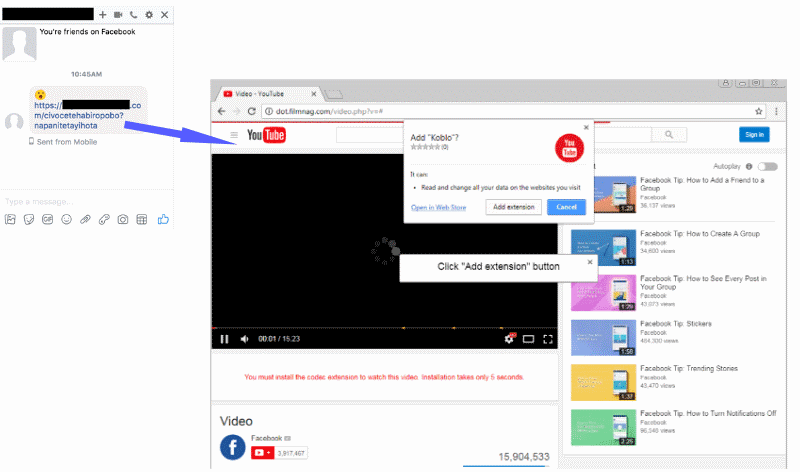
Image source: Bleeping Computer
After the plugin is downloaded, it scans the computer, and all digitally stored wallets for passwords, login details, and autosaved login forms. All collated login credentials are sent to FacexWorm’s servers.
However, according to Trend Micro, the phishing virus only works with some sites, including Google, MyMonero, and the controversial Coinhive mining software. A total of 52 identified sites makes the virus “active” with most being cryptocurrency sites or related to the sector.
Hereafter, things get interesting and raise obvious red-flags. On accessing cryptocurrency sites, the victim receives a pop-up which warns about a possible cryptocurrency scam; asking the user to send a small amount of ETH to “verify” their crypto-account.
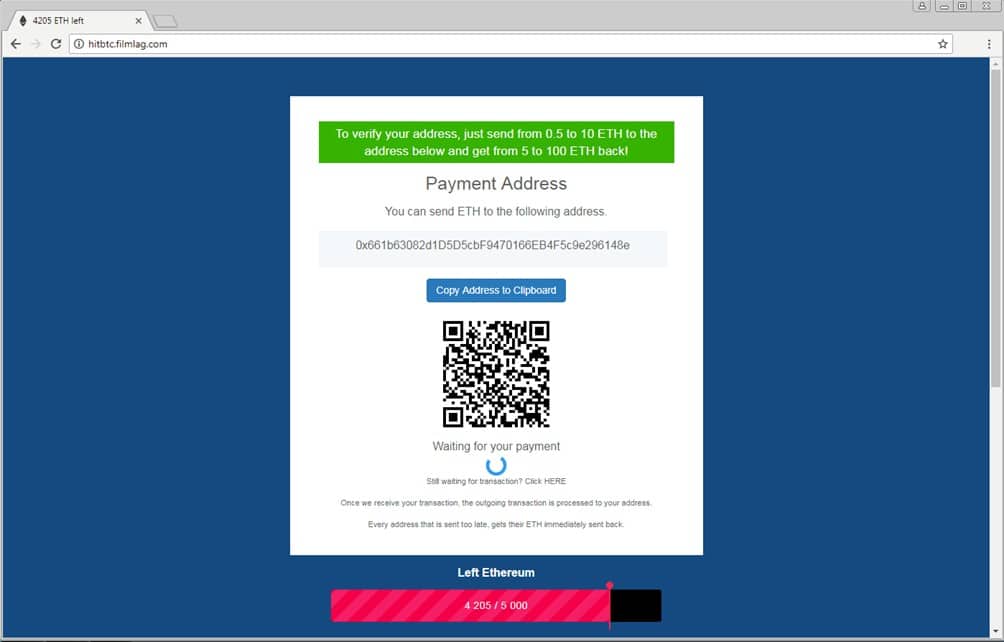
Image source: Bleeping Computer
Besides the phishing links and cryptojacking, the virus accessing crypto-trading platforms such as Poloniex, HitBTC, Bitfinex, Ethfinex, and Binance, and switches “recipient information,” thus gaining login details for user accounts, along with access to all their crypto-funds.
According to Trend Micro, the FacexWorm “switches” the recipient’s crypto addresses, i.e., if the victim tries to make a transaction, they are shown the hacker’s wallet address, instead of the intended recipient’s.
The virus can switch addresses of the following cryptocurrencies; bitcoin (BTC), bitcoin gold (BTG), bitcoin cash (BCH), dash (DASH), ether (ETH), ether classic (ETC), ripple (XRP), litecoin (LTC), zcash (ZEC), and monero (XMR).
Virus Shut Down Before Any Real Damage
Fortunately for the cryptocurrency enthusiasts, there’s no reason for panic, as Trend Micro reported the malware to Facebook and Google before it could harm users. Humorously, the elaborate and innovative malware could only capture a single paltry transaction of $2.49.
While Chrome acted swiftly and removed the malicious extension from its web-store, Facebook banned domains associated with the spam messages.