Feature, Bug or Backdoor? AntBleed Code Enables BitMain to Remotely Shut Down AntMiner
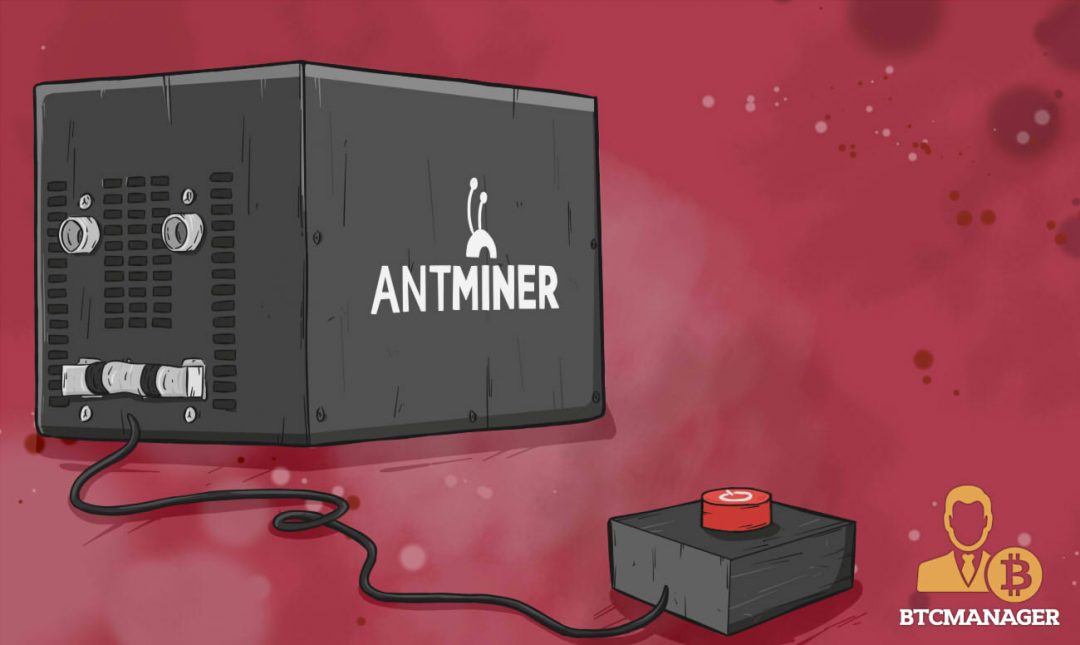
The scandals engulfing Chinese ASIC producer BitMain seem never to end. On April 26, a string of code in the AntMiner firmware was disclosed which can remotely shut down some of the mining machines. BTCManager talked with BitMain’s CEO Jihan Wu and a Canadian Miner; a Bug or Feature?
On April 26, the website AntBleed.com went online. It discloses a backdoor in new models of AntMiner, the most popular and efficient Bitcoin mining machine today, which is produced by BitMain, a Chinese ASIC company which has found itself in a growing storm of anger after it started to support controversial Bitcoin client Bitcoin Unlimited.
As the website explains, the software of AntMiner – which is open source, but pre-installed on the shipped ASICs – “checks-in with a central service randomly every one to 11 minutes. Each check-in transmits the Antminer serial number, MAC address, and IP address.” This secret connection to another server is bad, but by far not the worst part of the story; if the remote service returns “false,” the machine stops mining.
With this code, BitMain can shut down every AntMiner of the S9 series, which is every machine shipped after July 2016. It can also, the website continues, target specific miners by serial number or IP address, and shut them down. On top of this, the call to the remote server is not written very securely, so it could be subject to DoS attacks, advanced hacks or the action of large scale Anti-DoS-providers like CloudFlare, which can shut down miners. All this seems to be accurate beyond doubt.
Just a Protection against Miner Theft?
BTCManager reached out to Jihan Wu, CEO of BitMain. He explained:
“It is a feature that is under development and incomplete. It should help mining rig owners to track their rigs that are hosted by third parties. If it is stolen or hijacked, the owners will be able to use this feature to shut down the miner.”
In a statement on its website, BitMain explains the motivation of this development, “This was after more than one incident of miners being stolen from a mining farm or being hijacked by the operator of the mining farm.” The website lists incidents from 2014, 2015 and 2017 when several thousands of units of Antminers have been withheld by hosting service providers.
Due to technical problems the feature, however, has not been completed, Jihan Wu continues. The fact that a malicious party can patch the code very easily makes it in its current state worthless. He admits: “It is a bug to leave the code there, and the testing server has been shut down. We have removed it and released a new version of firmware.”
Not a Killswitch, but a Phone Home Feature?
Before we talked with Jihan Wu, we had a conversation with a Canadian Miner who mines several cryptocurrencies, including bitcoin and maintains a mixed set of different mining machines, including Antminer S9. His explanations are to some parts invalidated by BitMain’s statement, but they nevertheless shed some light of the nature of the code, and he provides an alternative explanation in case you mistrust BitMain’s explanation.
The miner spent the whole night probing the incident. He explained that the remote server the AntMiner software connects to has the DNS address auth.minerlink.com. Currently, this address is not activated, if you ping it, you get no response, but it is possible to locally redirect the DNS address to another IP address by editing files on your system. The AntBleed website provides a server miners can connect to, which runs a script that shuts down the miner if it is affected by AntBleed.
The Canadian Miner we talked with did not want to give an anonymous server his data, so he “put the AntBleed python script on one of a VM and tested it on the whole farm.” The result was that 12 percent of his miners stopped mining, which is most, but not all miners produced after the AntBleed Code was committed to the firmware. He could not provide a reason why some machines kept mining.
Asked if he thinks AntBleed is a remote kill switch for AntMiners, he answered: “I don’t think so, it is really the miners that phone home and get a reply from the server. And the phoning home address (auth.minerlink.com) is hardcoded in the source.” To hack this function, you need to manipulate the resolution of the DNS into an IP address on a large scale, which is not a trivial task but could be accomplished by governments or huge DNS providers or Anti-DoS-services like CloudFlare.
At the same time the miner, however, agreed that “Bitmain could shut down all machines that have the phone home feature. And yes, they could target specific customers if they record the IDs before delivering the miners.” On the other hand, the miner explained, “it is trivial to bypass; you just need to add one line to /etc/hosts”. The website AntBleed explains how you can deactivate the phone home function, which might be the patch Jihan Wu said makes the feature currently worthless.
Remote Control and Copyright
The Canadian miner agrees with BitMain that AntBleed is not implemented as a bug or a backdoor, but rather as a feature. He speculated about its purpose:
“A while ago I remember seeing Minerlink. This was BitMain’s idea of remotely controlling and monitoring your AntMiner machine through a website.”
The code disclosed by AntBleed “would phone home with machine specs (IP, MAC address, hashboard ID, etc).”
Since BitMain discontinued its Minerlink project, the website does not currently react to pings, which strongly indicates that the feature has not been used yet. Asked if the code is part of Minerlink, Jihan Wu however denied and explained that it is the opposite: “If the feature is completed, users will be able to set up and configure their own auth server and it does not have to go through Minerlink.”
“It is either a feature to allow you to shut down your miner through minerlink.com,” the Canadian miner continues, “but it can also be a way BitMain found to prevent people from copying his miners.” Similar as it is said that Google has a copyright protection for hardware which allows it to shut down Android machine with fake IDs, BitMain could use the phone home feature to detect and shut down faked hash boards.
Weaponize Code
The code is not malicious, the miner agreed with Jihan Wu:
“I don’t think there is a desire to weaponize it at all. Google can shut down all Android phones instantly. Do they do it? If it were really meant to be nefarious, they would have at least tried to obfuscate the code.”
For the miner, it is clear that this feature was instead “weaponized” by Core fans, which for the past few months have been on a crusade against BitMain because the mining company does not mine for SegWit, but chooses to use Bitcoin Unlimited. The design of the website, the timing of the disclosure and the massive activity on social media at this time indicate that the Miner may be right on this.
But this does not change the facts. The option to remotely shut down a miner, be it by BitMain or by large-scale hackers or governments, is not something that is desirable in the world of Bitcoin mining. Hopefully, the disclosure helps to deactivate it on a large scale. BitMain’s promise to remove it is a step in the right direction.
While on April 26 many people learned that mining is not as secure as they thought, you can conclude, mining has at the same time become more secure as a result of the AntBleed development.